AI-Amplified Operators
A systems-level reframing of work in an AI-saturated world, where humans and AI systems operate as a governed, resilient whole rather than as isolated tools and roles.
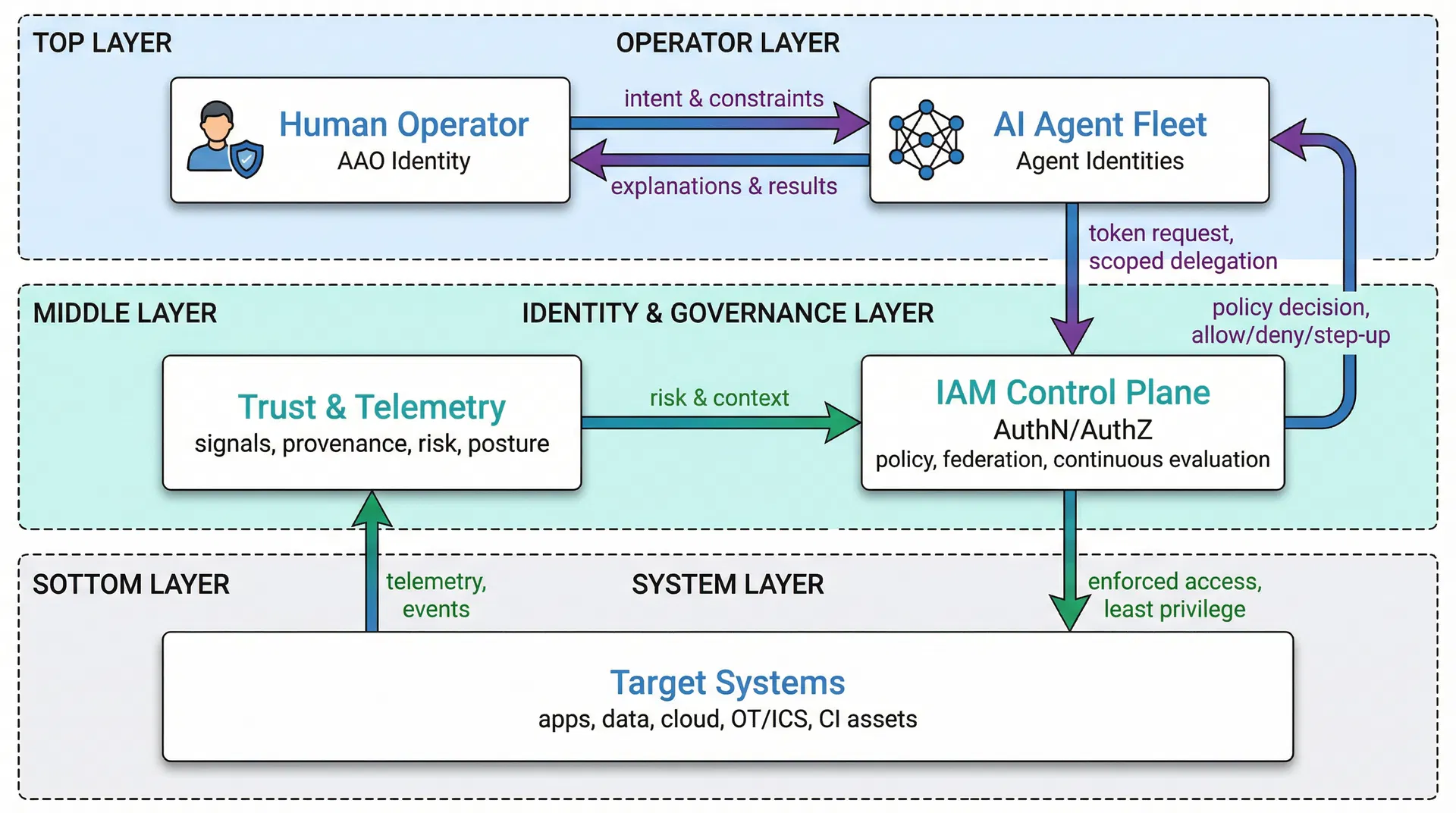
The AAO model reframes modern work around identity, intent, and outcomes. It formalizes the shift from role-bound specialists to identity-driven, AI-augmented operators—aligning directly with Zero Trust principles, agentic AI governance, and the A-DSRM methodology.
AAO Architecture
Identity-Governed Collaboration
Canonical Definition
"An AI-Amplified Operator (AAO) is a human operator whose cognitive, analytical, and execution capacity is persistently augmented by AI systems, operating across domains through identity, intent, and outcome, rather than static job titles."
Identity-centric
not tool-centric
Outcome-driven
not task-driven
AI-coordinated
not AI-assisted
Resilience-oriented
not efficiency-only
AAO Anchored to IAM
AAO only works because identity becomes the enforcement and trust fabric.
The human operator has a verifiable digital identity that serves as the root of trust for all delegated actions and AI agent coordination.
AI agents have scoped, governed identities with explicit authorization boundaries that prevent autonomous action beyond defined constraints.
Authorization is contextual, dynamic, and continuous—not static permissions but real-time policy evaluation based on risk signals.
Zero Trust is enforced across human–AI–system interactions, ensuring every action is verified, logged, and revocable.
Evolution Path: IAM → CIAM → Machine Identity → Agent Identity
AAO Taxonomy
Three primary operator archetypes demonstrate how AAO applies across software development, cyber defense, and infrastructure operations.
Scope
- Secure software design
- AI-assisted coding, testing, and threat modeling
- CI/CD and policy-as-code
Core Capabilities
- Delegates routine coding to AI agents
- Retains architectural and security authority
- Enforces least privilege for build and deploy agents
Security Posture
Related Artifact
AEGIS-M
Secure memory governance for AI-enabled systems
Scope
- Detection, response, and recovery
- SOC and IR operations
- Threat intelligence fusion
Core Capabilities
- AI agents triage alerts and correlate signals
- Human operator validates, escalates, or suppresses
- Response actions are policy-bounded
Security Posture
Related Artifact
PRAETORIAN-Q
Quantum-transition security framework
Scope
- Cloud, data center, OT/ICS, and critical infrastructure
- Zero Trust architecture
- Resilience engineering
Core Capabilities
- AI agents model system behavior and failure modes
- Human operator approves architectural changes
- Continuous posture optimization
Security Posture
Related Artifact
SVX-AD
AI/ML-based V2I security protocol
AAO vs Autonomous Agents
Understanding the critical differences between identity-governed AAO systems and ungoverned autonomous agents.
| Dimension | AAO (Identity-Governed) | Autonomous Agent |
|---|---|---|
| Authority | Bounded by IAM policies | Often tool/API-bound (keys) |
| Accountability | Strong (identity + provenance) | Weak (non-repudiation gaps) |
| Risk Control | Continuous verification, step-up | Usually static permissions |
| Blast Radius | Designed to be small | Frequently unbounded |
| Human Role | Operator w/ oversight | Supervisor after the fact |
| Delegation | Explicit + scoped | Recursive + emergent |
| Compliance | Auditable actions & intent | Hard to prove causality |
| CI/OT Safety | Supports fail-safe + revocation | Unsafe under adversarial inputs |
| Failure Mode | Safe degradation | Catastrophic cascade |
The AI-Amplified Operator Manifesto
We reject the myth of autonomous intelligence without accountability.
We reject static job roles in a dynamic, adversarial world.We assert that identity is the foundation of trust, and trust is the foundation of AI.
We believe humans must remain accountable operators, not passive supervisors.AI exists to amplify judgment, not replace responsibility.
Security is not a feature—it is a system property.The future belongs to operators who can reason, delegate, and govern AI safely.
The future belongs to AI-Amplified Operators.
AAO in Research & Teaching
AAO serves as a unifying construct across research, teaching, and practitioner guidance.
Within A-DSRM, AAO functions as a research abstraction enabling publishable questions:
- How does operator identity affect AI system safety?
- What failure modes emerge in AI-amplified operations?
- How do Zero Trust constraints shape human-AI collaboration?
AAO becomes the meta-persona for courses, reframing from "learn this tool" to "operate this system responsibly under uncertainty":
- CIS 3337 – Students as Secure AI Operators
- CIS 3351 – Students as AI-Amplified Defenders
- CIS 6358 – Students as Identity-Aware System Operators
AAO Certification Pathway
Develop the competencies to become an AI-Amplified Operator through structured training and certification.
- Identity-centric security foundations
- AI agent governance and delegation
- Zero Trust architecture principles
- Hands-on labs and assessments
Explore Related Frameworks
AAO integrates with other mental models and frameworks in Nsoh Research.

